In an era dominated by digital transformation, the adoption of cloud computing has become a cornerstone for businesses seeking agility, scalability, and cost-effectiveness. However, as organizations migrate sensitive data and critical operations to the cloud, the specter of security breaches looms large. The landscape of cloud security breaches has evolved over the years, presenting new challenges and requiring innovative solutions. In this comprehensive exploration, we will delve into the anatomy of cloud security breaches, the factors contributing to their rise, notable incidents, and the strategies employed to fortify cloud environments.
Contents
Understanding Cloud Security:
Before delving into the intricacies of cloud security breaches, it’s crucial to grasp the fundamentals of cloud security. Cloud security involves a set of policies, technologies, and controls designed to protect data, applications, and infrastructure in the cloud. Key elements include identity and access management, encryption, network security, and incident response. Cloud service providers (CSPs) play a pivotal role in securing the underlying infrastructure, while customers are responsible for safeguarding their data and applications.
Factors Contributing to Cloud Security Breaches:

- Misconfigured Cloud Settings: One of the primary reasons for cloud security breaches is misconfigured settings. As organizations move swiftly to adopt cloud services, misconfigurations in storage buckets, databases, and access controls can inadvertently expose sensitive information to the public internet.
- Inadequate Access Controls: Weak or mismanaged identity and access controls create opportunities for unauthorized access. Credential mismanagement, improper permissions, and lack of multifactor authentication contribute to security vulnerabilities that malicious actors can exploit.
- Insider Threats: Insiders with malicious intent or employees inadvertently causing security incidents pose a significant risk. Whether through intentional data theft or accidental exposure, insider threats can compromise the confidentiality and integrity of data stored in the cloud.
- Advanced Persistent Threats (APTs): APTs involve sophisticated, targeted attacks on organizations with the goal of unauthorized access and prolonged data exfiltration. Cloud environments are not immune to APTs, and attackers often exploit vulnerabilities in applications and infrastructure.
Notable Cloud Security Breaches:

- Capital One (2019): In one of the most high-profile incidents, a former employee of a cloud service provider exploited a misconfiguration in the web application firewall to gain unauthorized access to Capital One’s customer data. The breach exposed sensitive information of over 100 million customers.
- SolarWinds (2020): While not a direct cloud breach, the SolarWinds incident highlighted the interconnected nature of cybersecurity. Malicious actors compromised the software supply chain, affecting numerous organizations, including those relying on cloud services. This incident underscored the importance of securing the entire IT ecosystem.
- MongoDB Ransom Attacks: Several incidents involved ransom attacks on misconfigured MongoDB databases hosted on cloud platforms. Attackers exploited weak or absent authentication to access databases, encrypt data, and demand ransom payments for its release.
Strategies for Cloud Security:

- Continuous Monitoring and Auditing: Regularly monitoring and auditing cloud environments is critical for detecting and addressing security issues promptly. Automated tools can help identify misconfigurations, unauthorized access, and other anomalies.
- Education and Training: Human error remains a significant factor in security breaches. Educating employees on security best practices, the importance of strong passwords, and the risks associated with phishing attacks can mitigate the likelihood of breaches.
- Zero Trust Security Model: Adopting a zero-trust security model involves treating every user and device as untrusted, regardless of their location. This approach minimizes the potential damage caused by insider threats and ensures a robust security posture.
- Encryption and Tokenization: Implementing encryption for data at rest and in transit adds layer of protection. Tokenization can also be employed to replace sensitive data with non-sensitive equivalents, reducing the impact of a potential breach.
- Incident Response Planning: Developing and regularly testing an incident response plan is crucial for minimizing the impact of a security breach. Organizations should have a clear roadmap for identifying, containing, eradicating, recovering, and learning from security incidents.
- Multi-Factor Authentication (MFA): Implementing multi-factor authentication is a fundamental step in enhancing access controls. MFA adds an extra layer of security by requiring users to provide multiple forms of identification, such as a password and a temporary code sent to their mobile device, before gaining access to sensitive systems and data.
- Cloud-Native Security Solutions: Leveraging cloud-native security solutions designed for specific cloud platforms can enhance protection. These solutions often integrate seamlessly with cloud services, providing real-time threat detection, automated responses, and scalability to adapt to the dynamic nature of cloud environments.
- Regular Security Training and Simulations: Conducting regular security training for employees and simulating phishing attacks can improve awareness and resilience against social engineering threats. Human-centric security measures, combined with technical solutions, create a more robust defense against a wide range of potential breaches.
Conclusion:
As organizations continue to embrace the cloud, the importance of robust cloud security measures cannot be overstated. Cloud security breaches are not a question of if but when, making proactive measures and a holistic approach to security paramount. By addressing the root causes, staying informed about emerging threats, and implementing a combination of technological solutions and best practices, businesses can fortify their cloud environments against the evolving landscape of cyber threats. In the ever-changing realm of cloud security, staying vigilant and proactive is the key to safeguarding the digital assets that power the modern enterprise.
Conclusion: So above is the Unraveling the Complex Web of Cloud Security Breaches: Challenges, Trends, and Solutions article. Hopefully with this article you can help you in life, always follow and read our good articles on the website: Doshared.com
Related Articles

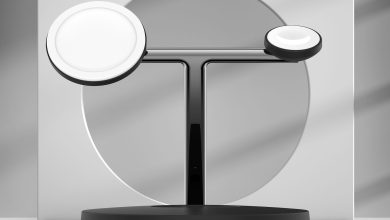
Assessment: Ugreen’s 4-Port GaN X USB-C Charger Presents As much as 100W Output in a Compact Design