Today, many businesses depend heavily on cloud-based services, and technology providers follow stringent privacy and data security regulations to safeguard users’ personal data. Organizations are helped and guided by Cloud Security Standards in order to ensure secure cloud operations. Doshared.com will provide some information about that.
Contents
What are cloud security standards?

Compliance rules have to change as infrastructure shifts to the cloud. Federal, international, municipal, and state security laws, regulations, and standards must now be complied with by cloud services and platforms.
ISO, PCI DSS, HIPAA, and GDPR compliance standards, among others, contain requirements specifically for cloud settings. Violations of legally required government regulations may result in sanctions like fines.
Specialized compliance standards have been developed in addition to generic compliance requirements, which can assist enterprises in achieving a secure cloud environment. These include the Cloud Security Benchmarks from the Center for Internet Security (CIS), the Controls Matrix from the Cloud Security Alliance (CSA), and the Cloud Architecture Framework.
Need for Cloud Security Standards

- Make sure the cloud is a suitable environment: As security and risk mitigation are the main issues, organizations must ensure that cloud computing is the right environment for their applications.
- To guarantee the security of sensitive data in the cloud: In order to comply with standards and regulations and ensure that sensitive data is secure in the cloud, organizations require a solution.
- No established, clear standard: Standards for cloud security are crucial since, previously, it was unclear what constituted a secure cloud environment. This makes it challenging for cloud service providers and consumers to specify what must be done to guarantee a secure environment.
- The requirement for a framework that covers all facets of cloud security: It is essential that companies adopt a
Cloud security standards are lacking.
- Due to the lack of proper cloud security standards, businesses and CSPs have been left to fumble while relying on an unending range of auditing needs, regulatory requirements, industry regulations, and data center standards to offer guidance on protecting their cloud environments.
- The Cloud Security Alliance’s fragmented strategy does not match the standards for “excellent security” as a result, making it more challenging to grasp than it initially appears to be.
Basic Standards for Cloud Security
The National Institute of Standards and Technology (NIST).

A government agency in the US called NIST develops measurements and standards to encourage competitiveness in the scientific and technological sectors. The Federal Information Security Management Act and the Health Insurance Portability and Accountability Act (HIPAA) (FISMA) are two US rules that the National Institute of rules and Technology (NIST) created the Cybersecurity Framework to comply with. According to their commercial value, assets should be classified and properly protected, according to NIST.
ISO-27017

A modification of ISO-27001 that includes clauses particular to cloud-based information security. Compliance with ISO 27017 should also be considered in addition to ISO 27001 compliance. The market has not yet been made aware of this standard. It makes an effort to provide more guidance in the area of information security for cloud computing. It serves as a supplement to the guidance offered in ISO/IEC 27002 and several other ISO27k standards, including ISO/IEC 27018 on the privacy implications of cloud computing and ISO/IEC 27031 on business continuity.
ISO-27018

A modification of ISO-27001 that includes clauses particular to cloud-based information security. Compliance with ISO 27017 should also be considered in addition to ISO 27001 compliance. The market has not yet been made aware of this standard. It makes an effort to provide more guidance in the area of information security for cloud computing. It serves as a supplement to the guidance offered in ISO/IEC 27002 and several other ISO27k standards, including ISO/IEC 27018 on the privacy implications of cloud computing and ISO/IEC 27031 on business continuity.
CIS controls

Internet Security Center (CIS) Controls, open-source regulations built on consensus, can assist organizations in safeguarding their systems. Before a decision is made, each check is thoroughly examined by a variety of experts.
Consult the CIS benchmarks tailored for certain cloud service providers to quickly receive a set of evaluations for cloud security. Use the CIS-AWS controls, for instance, a set of controls designed specifically for workloads using Amazon Web Services (AWS).
FISMA

All federal agencies and their contractors are obligated to protect information systems and assets in compliance with the Federal Information Security Management Act (FISMA). Under FISMA, NIST was given the responsibility to establish the framework security standards using NIST SP 800-53.
Cloud Architecture Framework
These frameworks can be seen as best practices guidelines for cloud architects because they usually address operational effectiveness, security, and cost-value considerations. AWS created this framework to help architects create workloads and apps for the Amazon cloud. This approach, based on a set of questions for the examination of cloud environments, provides customers with access to a trustworthy resource for architecture review.
General Data Protection Regulation (GDPR)

There are regulations protecting data protection and privacy for the European Union. Although this regulation solely pertains to the European Union, if you store or otherwise handle any personal information of EU citizens, you should be aware of it.
SOC Reporting
” Service and Organization Audits 2″( SOC 2) is a type of inspection of the functional procedures used by IT companies furnishing any service. SOC 2 reporting is a global standard for cybersecurity threat operation systems. The SOC 2 inspection Report demonstrates that your company‘s programs, styles, and controls are in place to misbehave with the five trust principles. Security principles mentioned in the SOC 2 inspection report include security, vacuity, recycling integrity, secretiveness, and confidentiality. However, prospective guests might want substantiation that you follow SOC 2 guidelines, If you give software as a service.
PCI DSS

The PCI DSS (Payment Card Industry Data Security Standard) stipulates a set of security requirements for all retailers who accept credit or debit cards. There is PCI DSS for companies that handle cardholder data. The PCI DSS outlines essential operational and technological requirements for protecting cardholder data. The PCI DSS standard aims to shield cardholders from credit card fraud and identity theft.
HIPAA
Parts of the US Congress’ Health Insurance Portability and Accountability Act (HIPAA), which was passed to protect people’s personal health information, deal especially with information security. HIPAA regulations must be followed by companies that handle medical data. The best option for information security is the HIPAA Security Rule (HSR). The HIPAA HSR outlines guidelines for safeguarding electronic personal health information that is generated, acquired, used, or maintained by a covered entity.
Risk assessments and risk management strategies are necessary for organizations subject to HIPAA laws to lessen threats to the accessibility, integrity, and confidentiality of the vital health data they manage. Assume your business uses cloud-based services (SaaS, IaaS, and PaaS) to send and receive health data. If this is the case, it is your duty to ensure that the service provider complies with HIPAA rules and that you have put best practices for managing your cloud settings into place.
CIS AWS Foundations v1.2
By following the CIS AWS Foundations Benchmark, any company using Amazon Web Services’ cloud resources can contribute to the protection of sensitive IT infrastructure and data. To assist enterprises in strengthening their information security, intelligence analysts created a collection of impartial, consensus-driven configuration benchmarks known as the CIS (Center for Internet Security) Benchmarks. CIS procedures are also used to strengthen AWS accounts so that a strong foundation may be created for conducting jobs on AWS.
ACSC Essential Eight
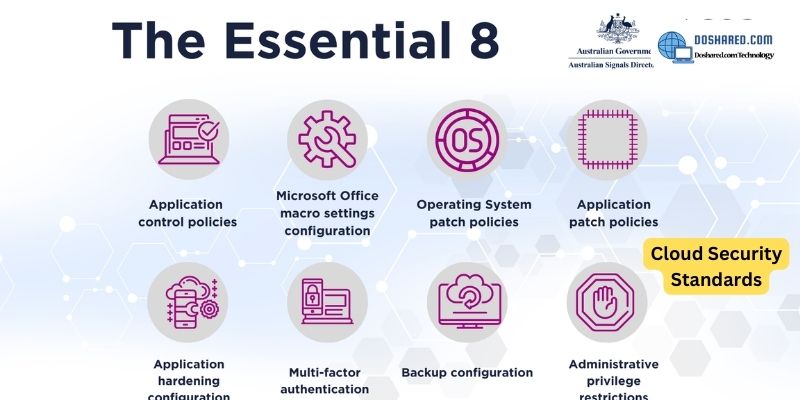
The ACSC Essential 8 is a list of eight cybersecurity risk management techniques for small and large businesses (also known as the ASD Top 4). The “Essential Eight Tactics” were designed by the Australian Signals Directorate (ASD) and the Australian Cyber Security Centre (ACSC) to enhance security controls, safeguard commercial computer resources and systems, and protect data from cybersecurity threats.
Conclusion: So above is the Cloud Security Standards That Every Business Should Know In 2023 article. Hopefully with this article you can help you in life, always follow and read our good articles on the website: Doshared.com




